With the ever-growing criminal activities like snatching of cars, bank robberies, murders and so forth, more and more steps are taking place to provide security and safety to people. It can be seen that specifically after major criminal activities, like September 11, people are diverting their attention towards the utilization of biometrics in order to authenticate the identifications of people. The old way of providing a national ID card or a special PIN code or password is taken over by biometric which extract information from a person's body itself (Rosenzweig, Kochems, & Schwartz, 2004). In other words, biometrics can be defined as being ways of distinguishing people from each other depending on their physical properties. Some widespread biometric technologies are inclusive of fingerprints, 3-D image of one hand, handwriting, voice recording, and scanning of iris and retina (BioVeriCom Incorporated, 2004).
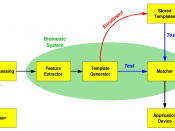
The usage of biometrics can be divided in two kinds.
The first kind is verification, in which the biometric helps in proving about a certain person if he really is what he says he is. This kind is also termed as "one-to-one" matching. The process of matching the real person with the biometric patterns of the person's verification on database takes less than a second. The second kind of biometrics is identification, which is termed as "one-to-many" matching. In this kind of biometrics, the shown biometric of a person is matched by all the biometric patterns presented in a database. This kind of biometrics is further divided in two kinds called positive and negative. In positive identification, it is made sure that the person who is providing his biometric is available in the database. On the other hand, in negative identification, it is made sure that the person's biometric is not available in the database (Rosenzweig, Kochems, & Schwartz, 2004).