Like the common cold, virtually countless variations of computer viruses exist. Unlike the biological viruses that cause the common cold, people create computer viruses. To create a virus, an unscrupulous programmer must code and then test the virus code to ensure the virus can replicated itself, conceal itself, monitor for certain events, and then deliver its payload-the destructive event or prank the virus can was created to deliver. Despite the many variations of viruses, most have two phases to their execution: infection and delivery.
To start the infection phrase, the virus must be activated. Today, the most common way viruses spread is by people running infected programs disguised as e-mail attachments. During the infection phase, viruses typically perform three actions:1. First, a virus replicates by attaching itself to a program files. A macro virus hides in the macro language of a program, such as Word. A boot sector virus targets the master boot record and executes when the computer starts.
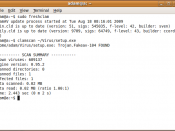
A file virus attaches itself to program files. The file virus, Win32. Hatred, for example, replicates by first infecting Windows executable for the Calculator, Notepad, Help and other programs on the hard disk. The virus then scans the computer to locate .exe files on other drives and stores this information in the system registry. The next time an infected file is run, the virus reads the registry and continues infecting another drive.
2. Viruses also conceal themselves to avoid detection. A stealth virus disguise itself by hiding in fake code section, which it inserts within working code in a file. A polymorphic virus actually changes its code as it infects computers. Win32. Hatred use both concealment techniques. The virus writes itself to the last file section, while modifying the file header to hide the increase file size. It also...