Executive SummaryIntroduction:Kudler Fine Foods (Kudler) is a one stop shop for gourmet cooks located in San Diego metropolitan area. The company has three locations La Jolla, Del Mar and Encinitas. The vision for this grocery store is to provide the freshest ingredients that will be needed for gourmet meals in one location at reasonable prices (Kudler, 2008). Kathy Kudler is dedicated to giving her customers the best shopping experience possible. The marketing strategies used by Kudler foods invite the customers into a fresh experience in cooking.
Kudler is in the process of developing a disaster recovery and business resumption plan. A disaster recovery plan also known as a business continuity plan (BCP) or business process contingency plan (BPCP), as a business continuity plan (BCP) or business process contingency plan (BPCP), is the method of analyzing disaster and assessing risk potential and business needs then building up a process which will keep the company's system and day to day business up and running with the minimum amount of downtime, by focusing on continuity (True Meridian, 2007).
The company uses this plan to keep the business profitable after a major event. The executive summary will mainly discuss the purpose of the plan, the scope, and the goals and objectives of the plan.
Purpose of the Plan:The main reason for Kudler's disaster recovery plan, is to have assurance that all contingencies in place will allow day-to-day functions to continue to work effectively if a severe occurrence or disaster that disrupts or threatens to disrupt services. The disaster can occur from natural disasters (tornados, floods, hurricanes/storms or fire), equipment failures, process failures, errors in judgment, and malicious acts (such as denial of service attacks, hacking, and viruses). Even with unpredictable and unpreventable occurrences, but contingency planning will help personnel to resume business.
The disaster recovery plan for Kudler mainly focuses on a set of actions the company takes in order to resume day-to-day business upon an occurrence. The disaster plans and policies include mandated actions to undertake for normal business functions, focusing on minimizing loss (MSU, 2008).
The disaster recovery plan consists of the following activities:Each department within the Kudler organization will maintain its own disaster recovery planning team. Each department will perform specific assigned duties to support the organizations Disaster Recovery Plan (DRP). The recovery team's roles and responsibilities include mandatory monthly meetings on updates to maintain the DRP. Duties also include enacting the DRP plan for effectiveness. Organizational team members will represent supervisory, technical and administrative experts for a cross representation of Kudler's organization. The table below represents Kudler's DRP organizational team with team members and the organizational responsibilities to maintain and operate the DRP.
Scope:In information technology a recovery/business resumption plan is relevant to an organization. The disaster recovery/business resumption plan for Kudler will describe the actions necessary in order for the company to presume operations within an allotted timeframe in the event of an emergency. Without warning the disaster recovery/business resumption plan can be activated whether Kudler is operating during normal business hours or during non operational hours. Kudler's disaster recovery/business resumption plan will ensure that all systems, facilities, vehicles are being maintained by information technology. This plan will also support the performance of remote locations in the event that the main facility is not equipped to function for normal business. The disaster recovery/business resumption plan will also provide management with continuity for decision making at Kudler if senior management or technical employees are unavailable.
Goals and Objectives:The primary objective of the Kudler's disaster recovery plan is to ensure the ability of the company maintain regular business if an occurrence that could disrupt day-to-day operations. The following are the goals of disaster recovery plan:â¢To maintain regular business because of occurring or impending disaster.
â¢The recovery of the normal operations.
â¢Backup and retrieval of data and forms.
â¢Install recovery data centers at different locations, where the backup should be scheduled.
â¢To have the backup in both forms hard copy and soft copy.
â¢Testing and drills.
Data integrity ensures that data is whole and complete, the condition of the data is maintained for future use and is an expectation of data quality. Data integrity can either be compromised by unauthorized changes to data internally or externally from the network, or can be accidentally altered due to transmission errors or a hard-disk crash. In order to preserve data integrity, Kudler must maintain current backups and a current disaster recovery plan including testing and drills, "control of access to data via security mechanisms, designing user interfaces that prevent the input of invalid data, usage of error detection and correction software when transmitting data" (Landa, 2008).
The primary causes of data integrity and security issues in Kudler's current setup are the possibility for data packet loss due to the current logical structure of the network and human error when entering data. Instituting new POS software that contains error controls against improper input into a database field which could damage and potential destroy some processes from working will alleviate the human-error aspect of the whole data integrity and security picture. Having a disaster recovery plan combined with off-site storage of critical data will help to keep data safe and able to recover in case of accidental mistakes or failed transfers due to uncontrollable circumstances such as weather.
Risk AssessmentIdentified Risks and Disaster Prevention MeasuresIdentifying, analyzing, potential risks, threats and hazards are all an integral part of performing a Risk Assessment, whether an organization experiences them internally or externally. An organization can be faced with numerous vulnerabilities, which can be associated with extreme weather, unforeseen power failures, equipment theft, internal and external breaches without unauthorized access, and failure to backup pertinent business information to name a few. In order for Kudler to alleviate those and other vulnerabilities the organization needs to perform a Risk Assessment. By Kudler performing a Risk Assessment the organization will be able to recognize, gather information related those threats, and address the issues proposed in order to improve the organizations exposure to vulnerabilities.
Functions such as human resource, customer service, and the company's information technology departments have become a major trend in outsourcing within major businesses. Benefits to outsourcing several processes and functions for companies is common, including critical risks that Kudler can face in outsourcing its IT functions. One major risk is the total reliance Kudler Fine Foods will have on its outside vendors should the vendor decide to terminate its client's relationship with Kudler.
Another risk would be the current IT department no longer having control of its physical security since its outsourced vendor would now handle it. Along with giving up physical control over their security processes, the IT department would lose physical access to its systems as well as the required frequencies needed to perform system backups. With outsourcing IT functions, it gives third party vendors access to the organizations entire information systems, which in turns increases the numbers of users who will have access to Kudler's system. With this increase, it raises the probability of Kudler's IT systems becoming breached. Any compromise to Kudler's information systems due to unauthorized access can alter and destruct its IT functions. All information including; employee records, financial data, payroll, and legal documentation can place Kudler in a vulnerable position if information is exposed to unwanted users.
As stated earlier, Kudler can be faced with vulnerabilities; however, all potential disasters or threats are impossible to describe. This Risk Assessment, takes into account both natural and human created disasters such as, flood, tornados and high winds, earthquake, malicious and terrorist actions, employee sabotage, aviation disaster, and fire.
Flood or Water DamageFlood or Water PrecautionsAlthough, flood or water damage has not been known to penetrate Kudler's locations in the past local and city storm sewers and drainage system outside have been installed to alleviate the potential threat of flood.
Flood RecommendationsWater detectors, drains and sump pumps will be operating and in place where deemed needed and tested often. Equipment and critical records should also be placed at the highest level at each location to avoid water damage.
Tornados and High WindsTornados and High Winds PrecautionsTornados and high winds are unpredictable and can potentially destroy or damage an entire location.
Tornadoes and High Winds RecommendationsLocal area weather systems should be monitored in the event of a server storm warning. Systems should be backed up in order to eliminate data loss and the interruption of daily activity at other locations.
EarthquakeEarthquake PrecautionsInspect and recommend retrofits where applicable.
Earthquake RecommendationsEarthquakes should be considered an increased risk, since Kudler is located in southern California, where earthquakes are most prevalent.
Computer CrimeComputer Crime PrecautionsKudler electronics are protected by security systems that are installed to protect against any unauthorized access or entry.
Computer Crime RecommendationsContinual updates and software upgrades will be accomplished on networking / firewall equipment to insure the most current protection against intrusion.
Terrorist action and sabotageTerrorist action and Sabotage PrecautionsThorough physical security using security personnel background checks, employee background checks, school identification cards and door locks for areas for authorized personnel are currently being used.
Terrorist actions and Sabotage RecommendationsKudler should explore options of alternative data backup solutions to increase security and help ensure information survival should such attacks occur.
FireFire PrecautionsFire Alarms are in place throughout Kudler Fine Foods. These are also present in the main level where the information technology operations are currently located. Fire Extinguishers have been placed throughout the buildingFire RecommendationsRegular inspections of the fire alarms and fire extinguishers are performed by the Operations and Maintenance department on a consistent basis.
Security AssessmentPhysical SecurityKudler has camera systems, guards and access control systems as protection methods for the facility. Physical security within the facility assesses mechanical, electronic and computer issues related to threats and hazards that may be a risk to the facility. Hazards and threats may come from other sources unrelated to common threats that may exist. "Hazards and threats may be from a secondary source. Neighboring offices or facilities may house materials or perform operations that generate hazards or threats for your operation. While Kudler does not have direct control over that type of hazard or threat, site vulnerability may be higher." (Disaster Management Training Programme (DMTP, 1994).
Personnel SecurityKudler provides annual security awareness training to all employees within the company. The training is provided to all users having access to any systems with Kudler, to ensure a proper information security posture. Kudler should install an account management, segregation of duties, monitoring, analysis, and reporting systems to augment the information security measures in order to ensure the insider and outsider does not alter access controls possibly allowing remote access.
Kudler security should take counter measures to ensure physical access is more controlled. Badges should be issued to all personnel in order to provide access only to authorized areas, and to monitor if someone is in an unauthorized location. This would eliminate dishonest employees from wandering into unauthorized areas.
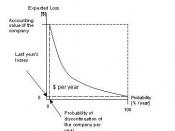
Information and Network SecurityIn order to determine the risks associated with Kudler's Information and Network Security of the organization the following ASIS International General Security Risk Assessment model (Figure 1) was used to determine those risks.
Figure 1 - ASIS International General Security Risk Assessment model (2003, pg. 9)By determining understanding and identifying the company's assets, vulnerabilities, probability of loss, impact of events, mitigated risks, implementation of options, and analysis of costs Kudler's most common risks were identified. Those risks consisted of hackers, internal breaches, e-mails, lack of anti-virus software and patches, data backup and FTP/Telnet. These vulnerabilities, along with their impact, recommendations/mitigations, and cost are detailed in (Exhibit 1.0).
Given the fact that Kudler is susceptible to the above risks along with others the company should implement a security blueprint. The blueprint should consist of requiring the IT department to implement frequent software and patch updates, limit the use of specific websites, such as social networking, streaming music, file sharing websites (Lime Wire), and any other sites that appear to be dangerous as seen fit by the IT department.
The IT department should also quarantine e-mails that are not recognized by customer or vendor related information, such as personal e-mails from outside sources with the exception of personal e-mails that are identified in the recipient's e-mail address book. All other e-mails will be quarantined where the employee will be able to retrieve the e-mails via an intranet site for approximately three days, if the sender is identifiable by the recipient. Otherwise the recipient will be able to reject those e-mails. Instances where e-mail attachments potentially have harmful viruses, malware, spyware an anti-virus software will automatically delete the potential threat prior to the recipient receiving the e-mail in their inbox. This software will also be installed on each operating system.
Other security measures that need to be taken into consideration is the use of company equipment, such as fax, machines, copiers, telephones along with personal equipment. The IT department along with management should implement guidelines where each employee has to participate in training security policies. These policies will indicated that personal drives, diskettes strictly prohibited. All other company equipment is strictly for internal business use and should not be take off of Kudler's premise, unless related to the employee's regular duties.
These vulnerabilities are just a few areas in which Kudler could potentially face during a disasters or threats. Given the fact that all threats are not easily identifiable a Risk Assessment of Kudler's assets and functions were reviewed to determine what necessary actions are needed for the company to continue operations after the effects of a disaster. Below is a chart (Exhibit 1.0) of Kudler's assets and functions and its description, threats and risks, recommendations and mitigations, impact from loss of sales, property and damage and increased expense. The chart also reflects Kudler's impact in dollars, how quickly the function or asset needed to be resumed, how critical the asset or function is as a business function and it weighted decision, which ranges from 0.1 to 1.0, with 0.1 being the lowest and 1.0 beginning the highest.
Exhibit 1.0Currently Kudler's operations rely heavily on paper, which consist of timesheets, vacation time, and inventory purchases for its locations. In the event that Kudler experiences a catastrophe at any of the three locations the company could stand to lose possession of its documentations. At each of Kudler's locations managers are responsible for providing the company's suppliers with purchase orders in to purchase goods from them. As a result the purchase order has to be faxed, mailed, or e-mailed to the respective vendor. If Kudler were to ever experience a power failure or the postal system ever lost Kudler' mail purchasing operations could come to a halt. By Kudler continuing to track vital information via paper records the company would have no way of producing back information for its records.
Another potential risk is the fact that Kudler's Point-Of-Sales (POS) system is not backed up on a regular basis. Kudler is currently using a Novell 4.11 server, which is located at each location. At this time the servers are not being backed up at a remote site location or a redundant system. Besides the company not being able to backup its servers the company also does not take advantage of backing up its payroll system, via Quick Books. In the event of a disaster the company would not have a means of being able to regenerated important data. Therefore, Kudler needs to ensure that backups are being conducted frequently and that procedures are being followed for the recovery Quick Books.
As stated earlier if Kudler is ever affected by natural disasters such as tornados, earthquakes, hurricanes or other typical server weather treats the company should have contingency plan which lays out procedures that need to be taken at each location. These procedures should be reviewed and tested on regular and adjusted as deemed necessary.
Other areas where Kudler could be affected are related to unauthorized access whether internally or externally, theft, or terrorism. In these instances employees may unknowingly down load viruses by opening e-mails from know senders or through an application download via the internet. Known e-mail senders could also potentially have their e-mail addresses altered, causing a spoofing affect. Another possibility would be opening e-mails from unknown sources, which can lead to spam mail being received on the organizations network.
On the other hand, employees could purposely sabotage an organizations files, records, or equipment. This can stem from the fact that the employee is either being bribed by a competitor, is committing identity theft, or is physically stealing equipment for their personal use. This type of threat can lead to the loss of data, corruption and inaccessible data, where operations have been disrupted for Kudler for an extended amount of time.
External access that is unauthorized as mentioned earlier can come through the form of a simple e-mail; however, external threats are not limited to e-mails. External threats are also related to hackers that are maliciously trying to access and attack Kudler's network, whether a competitor is stealing trade secrets, customer information, pricing matrix's, and earnings or to commit a criminal act of stealing sensitive information for their own use.
In order for Kudler to recover from natural disasters, human error, and intentional threats internally or externally, the company should implement preventative measure to mitigate the threats beforehand. By Kudler conducting a Risk Assessment the company is able to identify vulnerabilities and the steps that need to be taken to reduce the risk. In the event of a natural disaster Kudler should have a well thought out Business Contingency Plan (BCP), where measures have been taken to relocated employees, the property and equipment has been secured, customers have an alternate communication access, such as purchasing via the internet, where deliveries can be made from other locations, and where system back ups are stored offsite at a remote location or via a redundant system. If Kudler only experiences a power failure the company should use and uninterruptible power supply (UPS) at each location. Although, a power outage or natural disaster at the same time is unlikely for all three locations Kudler should have information backed up to a redundant system at a centralized location or either consider backing up data to diskettes, tapes, of portable hard drives. Depending on the severity of the natural threat the implementation of the BCP can reduce the amount of time the recovery process would take. This will only be as affective if the BCP is tested and updated on a regular basis.
Whether Kudler is attacked internally or externally the company will also need to implement preventative measures to mitigate potential threats. The first step in preventions is ensuring that firewalls and encryptions levels have been setup to secure Virtual Private Networks (VPN'S). Backups should be conducted frequently, antivirus software should be installed on each operating system for all locations, and user names and passwords should be implemented for POS terminals and operating systems. Along with these preventative measures Kudler's IT department should monitor and review logs of user activity and should consider installing an intrusion detection system and Secure Sockets Layer (SSL) protocols to secure session communications. The SSL protects FTP data that is transmitted by encrypting the data to maintain the confidentially of passwords and user names, which is also supported by digital certificates.
Disaster DeclarationLoss of FacilityKudler could be faced with several potential disasters or an actual disaster, but the impact is uncertain. However, in the event, where Kudler suffers a physical loss at one of its three locations this would not only be a negative impact where key personnel might be unavailable but the company would also suffer from major computer failures. This will cause a significant loss in business interruption. In this instance, an assessment must be made to determine the necessary procedures that will be implemented for unavailability, extent of damage, and loss according to the disaster recovery plan. In order for Kudler to recover within an acceptable amount of time several steps need to be taken by the disaster recovery team, which are as follows:Secure facilityPerform an assessment of damageSalvage efforts should be coordinatedRelocation of facilities as neededRepair or replace environmental equipment along with securityEnsure equipment has an adequate amount of powerThese steps along with others are not limited to Kudler's disaster recovery team; however, the steps will guide them through the recovery process. Depending on Kudler's deployment the recovery process will vary based on circumstances as follows:In instances, where the assessment proves that the facility only suffered a minor or temporary loss lasting only a few minutes or no longer than a day, the facility will not relocate.
If Kudler experiences a loss of more than one day, the facility will be relocated to a mobile site.
If one location is effected by a critical loss of business of multiple days or weeks, the store will relocate to a temporary alternative site.
Loss of LifeKudler's most valued asset are its employees and customers. In the event a "loss of life" occurs Kudler has to ensure that its employees are well protected, therefore, safety measure have to be taken and adhere to for those employees instead of protecting the company's equipment, property or data. During this event designated personnel should coordinate communication with the necessary parties, which would include call-trees, pagers, e-mails and other forms of communication. The following measures related to communication need to take place:Outside emergency personnel should be contacted in order to communicate the circumstances of the situation.
Ensure that employees are safeguarded in preserved area.
Notify appropriate family members or guardians of the situation.
Maintain detailed information related to the situation for later discussions with the insurance company, law enforcement, and emergency agencies for investigative purposes.
Damage AssessmentKudler's managers and designated personnel are responsible for the initial damage assessment of the company. In order for those in charge to be efficient all employees and available volunteer resources will assist in the assessment where needed. The assessment should begin as soon as possible after the impact of the emergency and Kudler's designated team members will begin its assessment. The following measures will need to be taken by the team:Assessment of preliminary damage to the facilities building(s), offices, and furniture should be coordinated.
The company's environmental support should be checked, such as the power supply and air conditioning.
The facilities security system and other protective equipment should be noted.
Communication via phone lines should be assessed along with computers, POS systems, software and networks.
An estimation of recovery time and usability of resources should be made.
The crisis management team should be notified with a report of the assessment along with recommendations.
Recovery OrganizationWithin the Kudler organization, each department will maintain its own disaster recovery planning team. Each group will perform specific duties in support of the organization DRP. General duties and responsibilities include meeting on specific dates during the calendar year to update and maintain the DRP. Duties also include testing the DRP plan for effectiveness. Finally organizational team members will represent a mixture of supervisory, technical and administrative experts for a cross representation of Kudler's organization. The following table is a current representation of Kudler's DRP organizational team with team members and the organizational responsibilities to maintain and operate the DRP.
Kudler Recovery OrganizationsRecovery Support Team OrganizationsTeam MembersResponsibilityCorporate Security RepresentativesCEO Kathy Kudler, Yvonne Reynolds (Dir. Store Ops), Harvey Stephens (Dir. Finance and Accounting), Kent Vesper (La Jolla Store Mgr), Laurie Priest (Del Mar Store Mgr), Juanita Lopez (Encinitas Store Mgr), Meredith Nguyen (IT Specialist), Matthew Vu (IT Specialist), Brenda Wagner (Admin Dir. and HR), Anne Shousha (Legal Counsel)Each Kudler team member will meet Bi-annually to discuss new and current security issues and will amend or delete the Disaster Recovery Policies and procedures. Including Legal, IT, Environmental.
Administrative Team RepresentativesCEO Kathy Kudler, Yvonne Reynolds (Dir. Store Ops), Harvey Stephens (Dir. Finance and Accounting), Kent Vesper (La Jolla Store Mgr), Laurie Priest (Del Mar Store Mgr), Juanita Lopez (Encinitas Store Mgr), Meredith Nguyen (IT Specialist), Matthew Vu (IT Specialist), Brenda Wagner (Admin Dir. and HR), Anne Shousha (Legal Counsel)Administrative Team Representatives will establish and maintain the Disaster Recovery Plan to include external organizational support, ID and assessing all risks, maintaining organizational and team responsibilities, training, business goals, corporate IT roles, environmental challenges. Public Relations, etc.
Human Resources RepresentativesBrenda Wagner (Admin Dir. and HR), Anne Shousha (Legal Counsel)Human Recourses Representatives will meet quarterly to amend the DR employee communications procedures and telephone tree.
IT Department RepresentativesHarvey Stephens (Dir Finance and Accounting), Meredith Nguyen (IT Specialist), Matthew Vu (IT Specialist)IT Department Representatives will meet quarterly to assess current and future business functions and technology. Procedures will include testing backup recovery procedures of current IT backup systems and facilities.
Facilities (Building Maintenance) Representatives Kent Vesper (La Jolla Store Mgr), Laurie Priest (Del Mar Store Mgr), Juanita Lopez (Encinitas Store Mgr), Meredith Nguyen (IT Specialist), Matthew Vu (IT Specialist)Kudler Facilities Representatives will develop procedures to maintain and update current and future facilities including backup facilities for Disaster Recovery. Procedure will include maintenance, communications and logistics of equipment.
Initial Response/Management TeamFollowing a reported disaster event, Kudler's initial response or recovery management team will be notified and conduct operations based on the roles in the table below. The administrative recovery team will then be notified to activate the final recovery team. All recovery operations will be directed by this team until all operations have been restored back to nominal business functions.
Kudler Initial Response Recovery Management TeamRecovery Team MemberOverall RoleCEO Kathy KudlerDirect DR teamYvonne Reynolds (Dir. Store Ops)Assist DR DirectorBrenda Wagner (Admin Dir and HR)Contact admin team and initiate communication planAdministrative TeamFollowing the activation of the recovery administrative team, the administrative team will then activate the final recovery team to begin final restorations of all business functions necessary to resume normal operations. This team is responsible for communications between the DRP management team and recovery team. Listed below are the team members responsible for administrative operations.
Kudler Recovery Administrative TeamRecovery Team MemberRoleBrenda Wagner (Admin Dir. and HR)Direct HR SpecialistCecilia Sams (HR Specialist)Contact Recovery Team and Coordination CommunicationsKent Vesper (La Jolla Store Mgr)Assist Admin Recovery Team DirectorLaurie Priest (Del Mar Store Mgr)Assist Admin Recovery Team DirectorJuanita Lopez (Encinitas Store Mgr)Assist Admin Recovery Team DirectorAnne Shousha (Legal Counsel)Direct Legal OperationsKudler Recovery TeamsThe final team responsible for the Kudler operations to restore Administrative, Technical and Facility Business functions is the Kudler Recovery Team. The Table below lists the team members responsible for recovery. All communications and coordination will be conducted through the Administrative Recovery Team.
Kudler Recovery TeamRecovery Team MemberRoleHarvey Stephens (Dir. Finance and Accounting)Direct Recovery Team LeadCecilia Sams (HR Specialist)Assists Direct Recovery Team Lead in Coordination of Recovery Plan and Voice communicationsMeredith Nguyen (IT Specialist)IT Security and Help Desk Admin (Restore IT)Matthew Vu (IT Specialist)IT System and Database Administrator (Restore IT)Kent Vesper (La Jolla Store Mgr), Laurie Priest (Del Mar Store Mgr), Juanita Lopez (Encinitas Store Mgr)Facility Maintenance, Personnel, and Physical Security, Voice communications MaintenanceMeredith Nguyen (IT Specialist), Matthew Vu (IT Specialist)Assist Maintenance Engineer is DR ResponsibilitiesTeam Members (Primaries and Alternates)In the event of a disaster all DRP team member will be responsible to designate an alternate team member. The alternate team member will have full authority and responsibility to conduct their assigned activities in the event the primary team member is unavailable. The primary team members with their respective alternates are listed in the following table.
Kudler DRP Team MembersResponsibilityPrimaryAlternateDRP Director \ System Owner CEO Kathy KudlerYvonne Reynolds (Store Ops)DRP Recovery Team Director System CustodianHarvey Stephens (Dir. Finance and Accounting)Kent Vesper (La Jolla Store Mgr)DRP Admin DirectorBrenda Wagner (Admin Dir. and HR)Juanita Lopez (Encinitas Store Mgr)Communication SpecialistCecilia Sams (HR Specialist)Arthur Stepka (Admin Specialist)Security Help Desk AdminMeredith Nguyen (IT Specialist)Matthew Vu (IT Specialist)System Database AdministratorMatthew Vu (IT Specialist)Meredith Nguyen (IT Specialist)Kudler Maintenance PersonnelKent Vesper (La Jolla Store Mgr)Laurie Priest (Del Mar Store Mgr), Juanita Lopez (Encinitas Store Mgr)Kudler LegalAnne Shousha (Legal Counsel)Brenda Wagner (Admin Dir. and HR)Telephone TreesIn the event of a disaster, most events will be reported to the Information Technology help desk and Maintenance Engineering departments within Kudler. These departments will then in turn communicate with the BCP Administrative Recovery team Communication Coordinator, who then contacts The DRP team lead and the recovery team will be notified to enact the DRP. Listed below is the communications or telephone tree response plan in the event of a disaster. The communication flow is from top bottom for the initial responses. Listed in the table below the Telephone Tree Contact Directory also includes the DRP Titles, Names and Phone Numbers. In the event a DRP member is not available, please see section 1.8 for the alternates to the positions.
Recovery ProceduresKudler's migration back to Normal Operations by the DR team is an essential part of the overall BCP. While facilities are conducting their backup of systems, recovery procedures must be taking place at the same time. Recovery strategies consist of getting what was damaged repaired or what was lost replaced or restored, whether the damage or loss involved Kudler's database, web, email, or infrastructure devices. Kudler has to ensure that these activities occur whether or not backup arrangements are activated. While migrating back to normal operations, Kudler should consider a decision on a system restoration. A plan execution checklist will help visualize the two critical decision periods.
Senior management should expect a self-assessment be conducted anytime a significant change occurs within the system. Harvey Stephens, Recovery Team lead will conduct emergency assessment meetings.
Return to normal operations:â¢Continue minimum essential operations;â¢Kudler Fine Foods site will phase down operations at alternate facilities.
â¢Each Kudler Fine Foods site will inform all personnel that an eminent danger no longer exist and for all personnel to return to normal operations;â¢Each Kudler Fine Foods site will conduct a "hot wash" of BCP operations, which will consist of lessons learned during the event.
Team ResponsibilitiesThe Kudler disaster recovery team will have 15 predefined team members and will meet at a specified location depending on the kind of severity level, the area and the physical location of the disaster. These severity levels are:â¢Level 1 disaster is a partial failure which can not be repaired within two hours. The location of the affected team's office for a disaster will be completed by video teleconference, or telephone to direct the operation by beginning the online backup server and notifying management of the extended outage until the systems are recovered and back online.
â¢Level 2 disaster is a scheduled outage shortly before or after a natural disaster. This disaster will be managed typically from the affected team's location. The team could use a site in the level 3 recovery. Three alternate sites will be maintained with server backups.
â¢Level 3 disaster outage occurs for more than three days. This level of disaster can occur where the backup team's locations are destroyed or have no backup ability. This level of disaster means the recovery team members will meet at an alternate site to begin the backup recovery process over the internet.
Application/Function PrioritiesKudler 's core business operations and functions are defined in the strategic and tactical planning process for the organization. Kudler's key core business units and business functions are outlined in the table below.
Core Business Units Business Functions⢠Financial 1. Payroll2. Accounts Receivable3. Accounts Payable⢠Manufacturing 1. Production2. Raw material storage3. Manufacturing equipment and buildings4. Key personnel5. Key Manufacturing Data Stores⢠Operations 1. Shipping/Receiving2. Equipment and buildings3. Construction, alterations, repairs4. Key Data Stores5. Key operations staff⢠Information Infrastructure 1. Key IT staff2 IT Equipment3 IT Date storesPolicy for Plan MaintenanceThe DRP will be reviewed as part of the DR exercise program. Changes in organizational structure, service to customers, and stakeholders will be made to the plan as they occur. Functions which can be anticipated will be addressed in the DR.
Testing approach, record and resultsThe Kudler DRP team within the organization is responsible for managing the DRP program; subsequently, there will be periodic reviews conduct within each recovery team and other appropriate personnel and managers to determine whether the DRP and the plans processes are adequately tested for currency, responsiveness, accuracy, and accessibility to the staff and business functions who utilize the DRP. This is particularly imperative should Kudler's business or security functions or activities change considerably. Such changes might require an alteration of the of Kudler's Disaster Recovery Plan. Kudler should periodically test the organization's Disaster Recovery Plans and Procedures to determine if the Recovery team designated as essential will allow DRP staff to function effectively in case of a disaster. The Kudler Management is and foremost responsible for managing the DRP program and staffing; as a result, the organization will work with all test participants to assess the results of the test and to make appropriate modifications where needed.
Personnel Training and ReplacementTraining of personnel is necessary to improve the resources of organization to execute its BCP and familiarize the organizations members with the essential functions that they might have to perform in an emergency. The viability of a BCP is dependent upon training of its personnel along with the evaluation of the results of the training programs. Major topics that will identify the issues and resources to implement an effective BCP education program are shown in the following chart.
PROGRAMS METHODS AUDIENCE FREQUENCY COSTOrientation ClassroomStudy material Senior Mgmt Yearly $5,000Refresher Intranet All EmployeesYearly $2,000Workshop BCP Team Monthly $12,000Outsourcing AssessmentFunctions such as human resource, customer service and the company's information technology departments have become a major trend in outsourcing within major businesses. Although many benefits exist in outsourcing several processes and functions for companies, Kudler can face several critical risks in outsourcing its IT functions. One major risk is the total reliance Kudler will have on its outside vendors should the vendor decide to terminate its client's relationship with Kudler.
Another risk would be the current IT department no longer having control of its physical security since it would now be handled by its outsourced vendor. Along with giving up physical control over their security processes, the IT department would lose physical access to Kudler's systems as well as the required frequencies needed to perform system backups. With outsourcing IT functions it gives third party vendors access to the organizations entire information systems which in turns increases the numbers of users who will have access to Kudler's system. With this increase, it raises the probability of Kudler's IT systems becoming breached. Any compromise to Kudler's information systems due to unauthorized access can alter and destruct all its IT functions. All information including; employee records, financial data, payroll and legal documentation can place Kudler in a vulnerable position if information is exposed to unwanted users.
Outsourcing Service Level Agreements and Costs Service Level Agreements (SLA) is primarily used in businesses as an effective tool used in controlling outsourced processes. The SLA will outline how both Kudler and its vendor of choice will work together. Kudler will need to consider the requirements of the SLA, list all the incentives and penalties to protect them, which will force its potential vendor to deliver results constantly. Once the internal analysis is concluded, Kudler should prepare a Request for Proposal (RFP) to solicit to potential vendors. Designing a RFP will leverage Kudler's purchasing power in obtaining the most favorable vendor in their selection process. Determining cost and quality of service is also a major factor in creating a SLA. If the vendor selected to perform the outsourced function are considered flexible and adaptable to the changes within Kudler's businesses, the company can potentially see a cost reduction savings of 30 - 50%. It should be Kudler's goal in wanting to maintain reduced long-term cost to better help guide them in maintaining stability and growth that will keep them ahead of its competitors. Seeking overall business improvements to Kudler's current operations rather than for its cost savings would help the company.
Several costs are associated with preparing a SLA which includes:Finding a reliable vendor.
How the outsourced process will be managed.
The training of staff for outsourced services.
Maintaining quality of service and retaining staff.
The amount of dependency required in transferring processes and functions to outsourced services.
Potential risks associated with increased costs of outsourcing are:Outsourcing the wrong process or function.
Not selecting the appropriate vendorInadequate and poorly written SLA's.
Personnel issues neglected and overlooked.
Not preparing and exit strategy for outsourced vendors.
Proper awareness of hidden costs.
If proper evaluations, measurements and analysis are not adequately conducted with Kudler in regard to outsourcing it can result in serious damage of the company's image, revenue, growth and reputation. Kudler must prepare for the potential risks and downfalls in order to become effectively acclimated with outsourcing. Having a proper strategic plan in place evaluating all the requirements, advantages and disadvantages of outsourcing will guide Kudler in making an effective decision to outsource its functions.
Disaster Recovery and Corporate TechnologyDisaster recovery planning is to maintain the business as usual and make sure that business continuity process is in place. Disaster recovery planning is vital for any business. A business continuity plan (BCP) includes planning for non-IT related aspects such as key personnel, facilities, crisis communication and reputation protection, and should refer to the disaster recovery plan (DRP) for IT related infrastructure recovery / continuity (Disaster Recovery, 2009). Most of the regulatory systems mandates escalate disaster recovery planning to a critical agenda item for information technology executives. Rigorous and realistic Disaster Recovery system plans and procedures are required to comply and mandates for information technology solutions applications.
A disaster recovery plan consists of testing failover and recovery strategies on the production datacenters, applications and network with production systems, personnel and procedures. Disaster recovery plan blue print covers any kind of local equipment failure to global disaster. Disaster recovery assessment "evaluates the impact of the failure of each process on all aspects of the organization" (Webb, 2007, ö2). Some of the important processes includes datacenters, client server/web based applications, databases, workstations etc.
According to Webb (2007, ö4), financial issues and revenue generation are important to consider, but the assessment goes beyond finances to evaluate impact to other areas such as public image, shareholder confidence, customer service, vendor relations, employee morale, consumer confidence and ability to comply with financial reporting requirements. The assessment identifies recovery time objectives (RTO) and recovery point objectives (RPO) based on the significance of each process to the strategic and tactical goals of the organization.
Disaster recovery planning starts with gathering all the requirements associated with all information technology components. "Once business requirements are established, the processes and procedures required to achieve the business requirements are identified" (Webb, 2007, ö6). Different types of disaster recovery implementations are available such as traditional solutions and emerging technology solutions. Magnetic tape and disks are the two leading media for data backup storage. Some of the necessary steps required to have complete business continuity process in place are near real-time backups, on-site virtual servers, imaging solutions, flexible restoration, secure remote storage, secure band width throttle, etc.
The real challenge with disaster recovery plan is switching the production network over to the backup network. According to Webb (2007, ö8), preparation for a live test is done in the test lab, where a production environment is reproduced through the four steps of network DR testing.
1.Create traffic profiles2.Establish impairment failure thresholds for applications3.Create network profiles4.Establish performance and quality metrics for the primary and backup systems"Recent technological advances have made it possible to replicate authentically a production network environment in a test lab. Real-world testing uses precision network emulators and a traffic generator/analyzer to create realistic and rigorous conditions for testing, tuning and verifying the performance of DR systems and subsystems prior to conducting the full scale test on the production network" (Webb, 2007, ö20).
ReferencesDisaster. (Recovery). Disaster recovery. Retrieved April 27, 2009, from Wikipedia Web site: http://wikipedia.org/wiki/Disaster_recoveryDMTP (1994). Disaster Assessment (2nd ed.). 1-54. Retrieved January 17, 2007 from:http://www.undmtp.org/english/Disaster_Assessment/Disaster%20Assess.pdfGeneral Security Risk Assessment. (2003), pg 9. Retrieved April 27, 2009, from ASIS International Web site: http://www.asisonline.org/guidelines/guidelinesgsra.pdfKudler Fine Foods. Apollo Group, Inc (2008). Kudler Intranet. Retrieved April 10,2009 from https//ecampus.phoenix.edu/secure/aapd/CIST/VOP/Business/Kudler/KudlerHome002.htmLanda, H. (2008). Planning for disaster. Associations Now, 4(13), p22-23. RetrievedApril 10, 2009 from EBSCO host databaseMSU, (2008). Michigan State University Disaster Recovery Planning, Step by Step Guide.
Retrieved April 13, 2009 from: http://www.drp.msu.edu/Documentation/StepbyStepGuide.htmTrue Meridian, (2007). Retrieved April 13, 2009 from: http://www.truemeridian.com/DRP.htmlWebb, C. (2007, October 15). Best Practices for Disaster Recovery Testing. Retrieved April 27, 2009, from Computer Technology Review Web site: http://www.wwpi.com/index.php?option=com_content&task=view&id=2894&Itemid=44