The Internet is infested with criminals and scoundrels. There's no point in sugar-coating that fact; prefacing an analysis of the Internet's inherent shortcomings by extolling its proven productive virtues is an exercise in triteness. For an organization to profitably exploit a global communications network is a relatively simple endeavor. The real challenge lies in securing the organization's assets from the thieves and vandals who troll that global network relentlessly. As a comprehensive overview of the Internet's adverse impact on information technology security is beyond the scope of this paper, the following analysis will examine some of the issues many organizations currently face in securing their networks from pervasive and relentless Internet-based attacks.
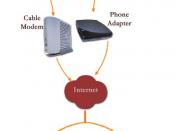
Network SecurityBy enabling Internet connectivity, organizations have opened their internal networks to various common forms of electronic communication, including email, web browsing, peer-to-peer file sharing, and instant messaging. To achieve some measure of protection against threats that exploit legitimate uses of Internet traffic to breach internal networks, organizations install firewalls as a perimeter defense tactic.
Firewall deployment is part of the canon of network security; however, according to Grochow (2005), firewalls cause many organizations to fall victim to a false sense of security, leading many to give short shrift to glaring security deficiencies that may exist within the network. Consequently, internal network users are often subject to a lower authentication threshold when attempting to gain access to the organization's applications and data. Since no firewall is completely secure, in the event of a breach, the hacker can typically traipse through the network with relative ease if there are no significant authentication obstacles in place. To shore up the security deficiencies, organizations can deploy applications that incorporate secure identity authentication standards (Grochow). Encrypting network traffic to protect sensitive data and messages is another viable option (Trombly, 2007).
In response...

Hmmm...Internet isn't really that bad
I cannot imaging a world with internet.. How inconvenient would that be?!
But security is really an big issue, especially areas that have impact on money.
Anyway, good job for the research on this topic. They are very useful information, and I can use them to overwhelm my teacher (who have no IT background) with all those technical terms and tools' name :P
0 out of 0 people found this comment useful.