Introduction
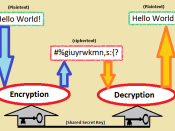
Software cryptography is coming into wider use. Systems like
Kerberos, PEM, PGP, etc. are maturing and becoming a part of the
network landscape [PEM]. These systems provide substantial
protection against snooping and spoofing. However, there is a
potential flaw. At the heart of all cryptographic systems is the
generation of secret, unguessable (i.e., random) numbers.
For the present, the lack of generally available facilities for
generating such unpredictable numbers is an open wound in the design
of cryptographic software. For the software developer who wants to
build a key or password generation procedure that runs on a wide
range of hardware, the only safe strategy so far has been to force
the local installation to supply a suitable routine to generate
random numbers. To say the least, this is an awkward, error-prone
and unpalatable solution.
It is important to keep in mind that the requirement is for data that
an adversary has a very low probability of guessing or determining.
This will fail if pseudo-random data is used which only meets
traditional statistical tests for randomness or which is based on
limited range sources, such as clocks. Frequently such random
quantities are determinable by an adversary searching through an
embarrassingly small space of possibilities.
This informational document suggests techniques for producing random
quantities that will be resistant to such attack. It recommends that
future systems include hardware random number generation or provide
access to existing hardware that can be used for this purpose. It
suggests methods for use if such hardware is not available. And it
gives some estimates of the number of random bits required for sample
Requirements
Probably the most commonly encountered randomness requirement today
is the user password. This is usually a simple character string.
Obviously, if a password can be guessed, it does not provide...